Computer Science 2018 — CSS Past Paper
NOTE: Other Paper is published separately.
NOTE: You can download this paper, the links are given at the end of the page.
FEDERAL PUBLIC SERVICE COMMISSION
COMPETITIVE EXAMINATION-2018 FOR RECRUITMENT TO POSTS IN BS-17 UNDER THE FEDERAL GOVERNMENT
COMPUTER SCIENCE, PAPER-I
TIME ALLOWED: THREE HOURS PART-I(MCQS): MAXIMUM 30 MINUTES PART-I (MCQS) MAXIMUM MARKS = 20 PART-II MAXIMUM MARKS = 80 NOTE:
- (i) Part-II is to be attempted on the separate Answer Book.
- (ii) Attempt ONLY FOUR questions from PART-II, by selecting TWO questions from EACH SECTION. ALL questions carry EQUAL marks.
- (iii) All the parts (if any) of each Question must be attempted at one place instead of at different places.
- (iv) Write Q. No. in the Answer Book in accordance with Q. No. in the Q.Paper.
- (v) No Page/Space be left blank between the answers. All the blank pages of Answer Book must be crossed.
- (vi) Extra attempt of any question or any part of the question will not be considered.
PART-II SECTION-I
Q. 2. (a) How many layers are in the TCP/IP stack? What are the names? (b) How digital evidences can be preserved from a crime scene. Write in details by taking examples of digital devices commonly used these days. (c) What are the responsibilities of Operating system kernel? (d) List down any four best practices for coding standards. (e) Why do modern processors use more power when their clock frequency is increased? (f) Ali is telling Ahmad that he is representing a -ve number and its most significant bit is 1, Ahmad immediately shouted you are representing numbers using 2’s compliment. True or False. And why? (g) If time slice is of 50 milliseconds and context switch requires a microsecond, how many processes can the machine service in a second? (4) (4) (3) (3) (2) (2) (2) Q. 3. (a) Write a program grade average calculator, User will input marks for five subjects and program will output the average of its marks. Print appropriate message on the base of its mark’s average e.g.; Well done, Keep it up, Better luck next time etc. (b) Given that i,j,k,n & m are integer variables. Write a condition such that: i- hello is only printed when, any of the following conditions are met: i is twice the value of j, j is smaller than k and less than n, or m is negative. inti,j,k,n,m; cin>>i>>j>>k>>n>>m; if( ) cout<<”hello”; ii. hello is only printed when i does not lies in the interval 6-9 inti; cin>>i; if( ) cout<< “hello”; (c) Write equivalent instruction to following instruction without the use of += operator: where w,z are integers. w+=2*z+4; (d) Predict the values of variables a & b after every instruction integer a=5 b=6 a=(b++) + 3; b=–a; (e) Complete the code such that it prompts the user for +ve number n. Then displays the output.(whatever the value of n is)(HINT: instead of triangles of stars its triangles of increasing numbers)[marks 1 2 3 4 . . . n 1 2 3 4 ..n-1 . . . . . . 1 2 1
for n=4 it will print
1 2 3 4
1 2 3
1 2
1
void main()
{
int n; cin>>n;
// your loops will go here }
(f) In following code replace the character at posth location in the string st with the ,character ch. For example in string helloworld replacing 2nd character with i would result in hilloworld
void main( )
{char st[15]; int pos; char ch;
int size=0;
cin>>st;
cin>>pos>>ch;
while(st[size]!='\0')
{
size++; // calculating length of current string
}
// write your code here }
(5)
Q. 4. Consider the inheritance hierarchy shown below. Each part of this question is independent.
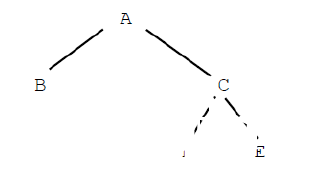
Computer Science 2018, Paper one, diagram 1
(a) In which class(es) would it make most sense to have protected members? Which class(es) would be able to access those protected members directly? (b) Which class(es) can access private members of class C directly? (c) Suppose class C contains a pure virtual function. Suppose we wish to instantiate objects of this hierarchy. Which class(es) are or could be abstract and which are concrete? (d) Consider the following list of classes: Car, SteeringWheel, Vehicle, Van, Minivan, AudioSystem, ParkingLot. Your task is to describe all of the is-a and has-a relationships between these classes. Include an inheritance hierarchy for all classes that fit. Fill in the table with is-a or has-a relationship while leaving the cells empty where no relation is applicable.
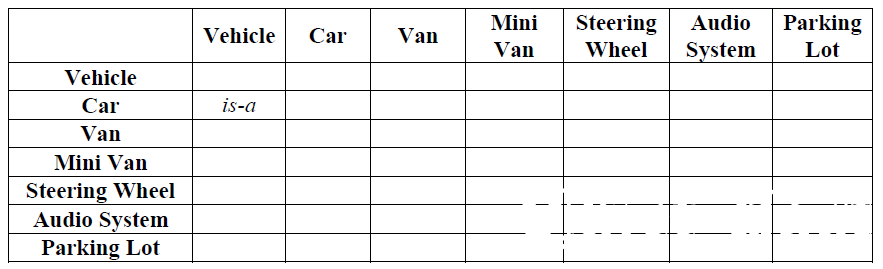
Computer Science 2018, Paper one, diagram 2
SECTION-II
Q. 5. (a) What is dangling pointer? (b) What data structure would employ to build a text editor and why? (c) Random insertion of nodes into a binary search tree would result in what types of tree shape. Elaborate. (d) How would you modify a link list based queue so that first and last node can be accessed in a constant time regardless of data nodes in the queue? (3) (5) (7) (5) Q. 6. (a) Define balanced tree both for AVL and Binary search tree. (b) What is informed or heuristic search what type of algorithm is used to do such a search? (c) Differentiate between graph and trees. Which is special case of the other? (d) Explain what type of problems can be solved by genetic algorithm. (4) (6) (5) (5) Q. 7. (a) Outline the difference between software verification and software validation. (b) Give an outline of the unit testing process for verification. (c) Agile Development is a process that values responding to change over following a plan. Discuss three issues a Software Engineer should be mindful of when adopting this approach during software development. (d) What type of project is not suited to incremental methods? (e) Outline the difference between Black box and White box testing. (4) (4) (4) (4) (4) Q. 8. (a) What is the difference between lexers and parsers? (b) Write a grammar (BNF) for the language of palindromes. (c) Here DFA is given for the language L find the DFA for L2
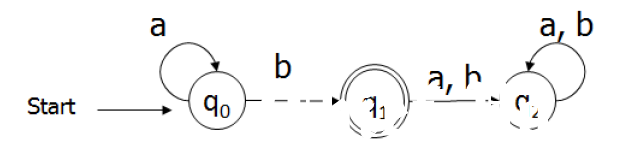
Computer Science 2018, Paper one, diagram 3
(d) Convert the following DFA to a RE:
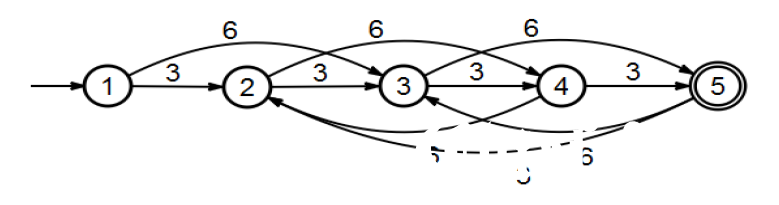
Computer Science 2018, Paper one, diagram 4
(5) (5) (5) (5)
**********
You can Download this Paper from Google Drive or Dropbox.
Download from Google Drive: Click Here
Download from Dropbox: Click Here