Computer Science 2021, Paper 2 — CSS Past Paper
NOTE: Paper one is published separately.
FEDERAL PUBLIC SERVICE COMMISSION
COMPETITIVE EXAMINATION-2021 FOR RECRUITMENT TO POSTS IN BS-17 UNDER THE FEDERAL GOVERNMENT
COMPUTER SCIENCE, PAPER-II
TIME ALLOWED:
- THREE HOURS
- PART-I (MCQS): MAXIMUM 30 MINUTES
- PART-I (MCQS) MAXIMUM MARKS = 20
- PART-II MAXIMUM MARKS = 80
NOTE:
- (i) Part-II is to be attempted on the separate Answer Book.
- (ii) Attempt ONLY FOUR questions from PART-II, by selecting TWO questions from EACH SECTION. ALL questions carry EQUAL marks.
- (iii) All the parts (if any) of each Question must be attempted at one place instead of at different places.
- (iv) Write Q. No. in the Answer Book in accordance with Q. No. in the Q.Paper.
- (v) No Page/Space be left blank between the answers. All the blank pages of Answer Book must be crossed.
- (vi) Extra attempt of any question or any part of the question will not be considered.
PART – II
SECTION – A
Q. No. 2.
(a) The addressing in a typical instruction format are done by using different addressing modes. Examine any live addressing modes with an example based on the contents of address field, actual address and contents of memory location.
(b) The decimal value of address field in an instruction is 120. The addressing mode of the machine’s architecture is register direct and register indirect addressing. Calculate the address of corresponding operand.
(c) Compare the set of addressing modes of RISC and C1SC machines. Give one example of addressing modes used in RISC and CISC respectively.
Q. No 3.
Memory managed by BITMAP is shown below:
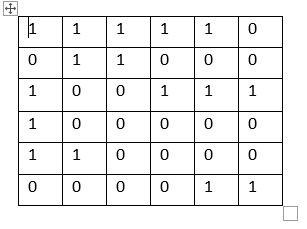
Question No. 2, Computer Science, Paper 2, CSS 2021
(a) Show properly filled memory according to the BITMAP where memory, index starts from zero.
(b) Insert a page H of size 1 allocation units in memo, drawn in part ‘a’ using first-fit algorithm. Redraw memory and the BITMAP after insertion.
(c) Now insert another page K of size 2 allocation units in memory drawn in part ‘b’ using next-fit algorithm. Redraw memory und the BITMAP after insertion. (6)
(d) Use linked list data structure for the above memory mapping (Only give equivalent figure). (5)
(e) Use hash table to keep track of active pages in the above memory (Only give figure).
Q. No. 4.
Do as directed:
(a) Calculate effective memory access time using following data: (3)
- TLB hit ratio is 85%
- TLB access time=20nsec
- Memory access time = 115nscc
Effective memory access time = Hit rate * (TLB access time + Mem access time) + (1-Hit rate) (TLB access time + Process_table access time+ Mem access time) (4)
(b) Consider a logical address and physical address of 31 and 22 bits respectively. What will be total logical and physical address space?
(c) Does resource allocation graph shown below consist of a deadlock or not? Justify with reason.
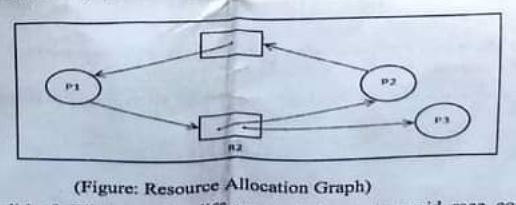
Question No. 4, Computer Science, Paper 2, CSS 2021
Q. No. 5.
(a) Compare Transmission Control Protocol and User Datagram Protocol. How they are used m wireless networks?
(b) What mechanism is used by TCP to protect from miss delivery?
(c) Calculate the TCP window size to fully utilize the line on which WAN link is 2 Mbps and RTT between source and destination is 300 msec.
SECTION-B
No. 6.
Consider the following database schema write the relational algebra expression the following queries.
- Students (Stu_Reg, Stu_Name, Stu_Address)
- Instructor (Ins_ID, Ins_Name. Ins_Dept_ID)
- Course (Cr_Code, Cr_)Title. Cr_Cr_hours)
- Dept (Dept_ID, Dept_Name)
- Results (Res_Stu_ Reg, Res_Cr_Code, Res_marks, Res_Ins_ID, Res_Grade)
(a) Write relational algebraic expression for:
- (i) To display all the students details in section BSSE.
- (ii) To display all Instructor Names and their respective Department Name (if an instructor is not assigned any Dept his name should be displayed as we).
- (iii) To display Stu_Reg, Stu_Name, Cr_Code, Cr_Title and Res_Marks for students who got 75 or more marks.
- (iv) To display Res_Stu_Reg, Ins_Name, Res-Grade. for Instructors whose Dcpt_ID is 1.
(b) What is the concept of gerund in database? Give one example of gerund. Is this essential to eliminate gerunds from the database? If yes, and if no, why?
Q. No. 7.
(a) Write code/pseudo code to locate all of the large boxes in the image below using morphological image processing.

Question No. 7, Computer Science, Paper 2, CSS 2021
(b) Is there a need for more than 1 color model? Mention different colors models and there uses.
(c) Explain CMY color model, as use and how is it different from CMYK?
Q. No. 8.
(a) Analyze the code and draw resulting table as drawing on the paper
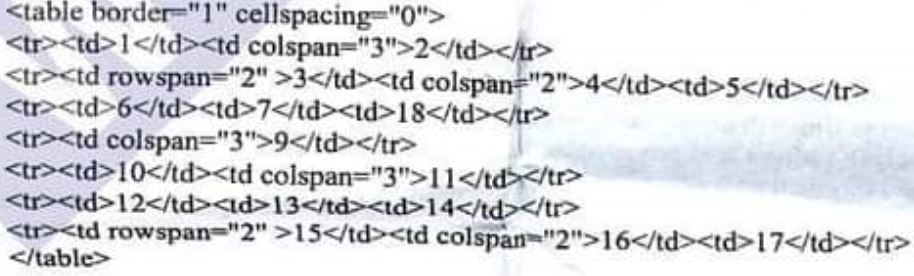
Question No. 8, Computer Science, Paper 2, CSS 2021
(b) What is the role of requirement engineering in web engineering? List functional and non-functional requirements for a website. (5)
(c) What are different security mechanisms used for encrypting the contents of a website? Explain one in detail. (6)
**********