Computer Science 2019 — CSS Past Paper
NOTE: Other Paper is published separately.
NOTE: You can download this paper, the links are given at the end of the page.
FEDERAL PUBLIC SERVICE COMMISSION
COMPETITIVE EXAMINATION-2019 FOR RECRUITMENT TO POSTS IN BS-17 UNDER THE FEDERAL GOVERNMENT
COMPUTER SCIENCE, PAPER-I
TIME ALLOWED: THREE HOURS PART-I(MCQS): MAXIMUM 30 MINUTES PART-I (MCQS) MAXIMUM MARKS = 20 PART-II MAXIMUM MARKS = 80 NOTE:
- (i) Part-II is to be attempted on the separate Answer Book.
- (ii) Attempt ONLY FOUR questions from PART-II, by selecting TWO questions from EACH SECTION. ALL questions carry EQUAL marks.
- (iii) All the parts (if any) of each Question must be attempted at one place instead of at different places.
- (iv) Write Q. No. in the Answer Book in accordance with Q. No. in the Q.Paper.
- (v) No Page/Space be left blank between the answers. All the blank pages of Answer Book must be crossed.
- (vi) Extra attempt of any question or any part of the question will not be considered.
PART – II SECTION – I
Q. 2. (a) Give a detailed note on a revised BSD 3-clause license. Also name 5 softwares using this license. (b) How do artificial intelligence may facilitate us in improving cyber security? (c) What are the main parts and phases of a computer virus program? (10) (5) (5) (20) Q. 3. (a) See the following C++ program to declare whether an input number is a prime number or not. Identify the logical errors in the given program (if any). Give your correct statement(s) exactly at the same line number. 1. n, i; 2. bool is Prime = false; 3. cout<< “Enter a positive integer: “; 4. cin>> n; 5. for(i = 1; i< n / 2; ++i) 6. { 7. if(n /i == 0) 8. { 9. is Prime = false; 10. break; 11. } 12. } 13. if (is Prime) 14. cout<< “This is a prime number”; 15. else 16. cout<< “This is not a prime number”; (b) What is the difference between call by value and call by reference? (c) What is the role of preprocessor directives? Give three examples in C++. (10) (5) (5) (20) Q. 4. (a) How do the OOP paradigm can be associated with the real-world problems? Explain. (b) Discuss critical reasons given by the professionals for not supporting the OOP paradigm. (10) (10) (20) Q. 5. (a) Discuss the security issues associated with the cloud computing. (b) What is bit twiddling? Give brief description. (c) An image is a representation of some information. Discuss how does a computer represents an image internally? Name different algorithms used to extract features from images. (10) (5) (5) (20)
SECTION-B
Q. 6. (a) Discuss the limitations of genetic algorithms. (b) What is AVL tree? Under what condition, a binary tree becomes AVL tree? (c) Consider the following graph. Find out the sequence of edges added to the minimum spanning tree using Kruskal’s algorithm.
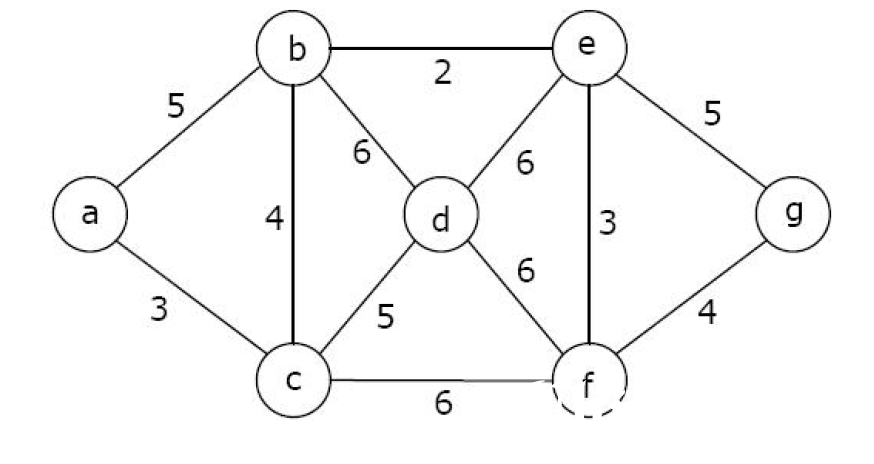
Computer Science 2019, Paper one, graph 1
(10) (5) (5) (20) Q. 7. (a) Discuss the architecture of aspect-oriented system. (b) Briefly discuss the motivation for aspect-oriented programming. (c) What is the significance of quantification and obliviousness? (10) (5) (5) (20) Q. 8. (a) Write down the major steps involved in code generation. (b) How would you optimize a loop? Describe the techniques briefly. (c) Differentiate machine-dependent optimization and machine-independent optimization. (10) (5) (5) (20)
**********
You can Download this Paper from Google Drive or Dropbox.
Download from Google Drive: Click Here
Download from Dropbox: Click Here